What is digest of a message
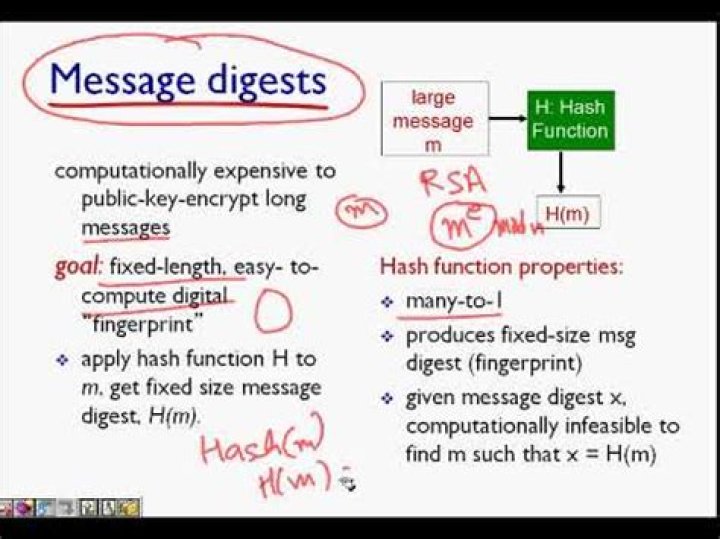
A message digest is a fixed size numeric representation of the contents of a message, computed by a hash function. A message digest can be encrypted, forming a digital signature. Messages are inherently variable in size. A message digest is a fixed size numeric representation of the contents of a message.
What is message digest size?
As shown in Table 1, all four of the algorithms are iterative, one-way hash functions that can process a message with a maximum length of 264- to 2128-bits to produce a 160- to 512-bit condensed representation called a message digest.
What is message digest in Java?
Message digests are secure one-way hash functions that take arbitrary-sized data and output a fixed-length hash value. A MessageDigest object starts out initialized. The data is processed through it using the update methods. At any point reset can be called to reset the digest.
What does Digest () do?
Digest algorithms, also known as cryptographic hash functions, transform an arbitrarily large block of data into a fixed-size output, usually much shorter than the input. They have a variety of applications in cryptography.What message digest is used as an MD?
MD5 is the Message Digest algorithm 5, created by Ronald Rivest. It is the most widely used of the MD family of hash algorithms. … MD6 is the newest version of the MD family of hash algorithms, first published in 2008.
What is meant by message digest give an example?
A message digest is a cryptographic hash function containing a string of digits created by a one-way hashing formula. Message digests are designed to protect the integrity of a piece of data or media to detect changes and alterations to any part of a message. … One message digest is assigned to particular data content.
What is digest in security?
Digest Access Authentication is a way for service providers to verify a person’s credentials by using a web browser. Specifically, digest access authentication uses the HTTP protocol, applying MD5 cryptographic hashing and a nonce value to prevent replay attacks.
Is MD5 still used?
MD5 is still being used today as a hash function even though it has been exploited for years. … Hash functions have variable levels of complexity and difficulty and are used for cryptocurrency, password security, and message security. Following in the footsteps of MD2 and MD4, MD5 produces a 128-bit hash value.Is message digest algorithm?
A message digest algorithm or a hash function, is a procedure that maps input data of an arbitrary length to an output of fixed length. Output is often known as hash values, hash codes, hash sums, checksums, message digest, digital fingerprint or simply hashes.
Where is Message Digest used?Message Digest is used to ensure the integrity of a message transmitted over an insecure channel (where the content of the message can be changed). The message is passed through a Cryptographic hash function.
Article first time published onHow does Message Digest algorithm work?
The MD5 (message-digest algorithm) hashing algorithm is a one-way cryptographic function that accepts a message of any length as input and returns as output a fixed-length digest value to be used for authenticating the original message.
What is hex digest?
hexdigest() : the digest is returned as a string object of double length, containing only hexadecimal digits. This may be used to exchange the value safely in email or other non-binary environments.
What is Message Digest Tutorialspoint?
Message Digest (MD) It is a 128-bit hash function. MD5 digests have been widely used in the software world to provide assurance about integrity of transferred file. For example, file servers often provide a pre-computed MD5 checksum for the files, so that a user can compare the checksum of the downloaded file to it.
Why is hashing used?
Hashing is a cryptographic process that can be used to validate the authenticity and integrity of various types of input. It is widely used in authentication systems to avoid storing plaintext passwords in databases, but is also used to validate files, documents and other types of data.
How do you make digestion?
- Go to the page that has news you want to send in a digest. …
- In the News section, select See all. …
- Select Email a news digest.
- Using the checkboxes on the left, select the news stories to include in your digest.
- At the bottom right of the screen, click Next.
Are Ripemd still used?
GeneralDigest sizes128, 160, 256, 320 bits
What level of protection does the MD5 offer for Passwords?
Unfortunately, MD5 has been cryptographically broken and considered insecure. For this reason, it should not be used for anything. Instead, developers should switch to the Secure Hash Algorithm or a Symmetric Cryptographic Algorithm.
Which is the original message before transmission?
The original message is called the plaintext message. The encrypted message is called the ciphertext message.
What is Digest realm?
Digest access authentication is one of the agreed-upon methods a web server can use to negotiate credentials, such as username or password, with a user’s web browser. … Technically, digest authentication is an application of MD5 cryptographic hashing with usage of nonce values to prevent replay attacks.
What is enable digest authentication?
Digest authentication is a method of authentication in which a request from a potential user is received by a network server and then sent to a domain controller. … If the user’s response is of the correct form, the server grants the user access to the network, Web site or requested resources for a single session.
What is signed digest?
Signing the Digest The sender creates a miniature version (digest) of the document and then signs it, the receiver checks the signature of the miniature version. The hash function is used to create a digest of the message.
What is the order of finding two messages having the same message digest?
Explanation: The difficulty of coming up with 2 messages having the same message digest is on the order of 2256. Explanation: The underlying structure of the SHA-3 algorithm is referred to as Sponge construction. 6. SHA-3 allows variable length input and output.
What encrypted traffic?
Traffic encryption, known officially as hypertext transfer protocol secure (HTTPS), is a method of securing the transmission of information to and from a website. … To communicate with a website through a secure, encrypted channel, you use a URL (website address) that begins with https rather than http.
What is a message digest quizlet?
Terms in this set (12) message digest, hash, algorithm. takes a string of text (the contents of your file or messages) and produces a fixed-length set of hexadecimal characters.
Is sha256 secure?
SHA-256 is one of the most secure hashing functions on the market. The US government requires its agencies to protect certain sensitive information using SHA-256. … Second, having two messages with the same hash value (called a collision) is extremely unlikely.
What is checksum verification?
A checksum is a value used to verify the integrity of a file or a data transfer. In other words, it is a sum that checks the validity of data. Checksums are typically used to compare two sets of data to make sure they are the same.
What is MD5 and SHA1?
Both MD5 stands for Message Digest and SHA1 stands for Secure Hash Algorithm square measure the hashing algorithms wherever The speed of MD5 is fast in comparison of SHA1’s speed. However, SHA1 provides more security than MD5. … Some features of hash algorithms are given below: The has functions can’t be restrained.
What is hash function algorithm?
A hashing algorithm is a cryptographic hash function. It is a mathematical algorithm that maps data of arbitrary size to a hash of a fixed size. A hash function algorithm is designed to be a one-way function, infeasible to invert. … Every change to a message, even the smallest one, should change the hash value.
How does a message authentication code work?
A message authentication code (MAC) is a cryptographic checksum on data that uses a session key to detect both accidental and intentional modifications of the data. A MAC requires two inputs: a message and a secret key known only to the originator of the message and its intended recipient(s).
How can you transfer a message securely using hash function?
Generate a hash (which can also be a message authentication code), attach the hash to the key, encrypt that product using the public key of the recipient. Then email it to them. Upon receipt the person first uses their private key to decrypt the message.
How does MD5 work example?
MD5 processes a variable-length message into a fixed-length output of 128 bits. The input message is broken up into chunks of 512-bit blocks (sixteen 32-bit words); the message is padded so that its length is divisible by 512. The padding works as follows: first, a single bit, 1, is appended to the end of the message.