What is Open authentication
Open authorization (or OAuth for short) is a type of token-based authentication that allows organizations to share information across third-party services without exposing their users’ usernames and/or passwords.
What is an open authorization?
OAuth (Open Authorization) is an open standard authorization framework for token-based authorization on the internet. … It acts as an intermediary on behalf of the end user, providing the third-party service with an access token that authorizes specific account information to be shared.
What exactly is OAuth open authorization?
OAuth (Open Authorization) is an open standard for access delegation, commonly used as a way for Internet users to grant websites or applications access to their information on other websites but without giving them the passwords.
What is OpenID Connect used for?
OpenID Connect lets developers authenticate their users across websites and apps without having to own and manage password files. For the app builder, it provides a secure verifiable, answer to the question: “What is the identity of the person currently using the browser or native app that is connected to me?”What is OpenID and oauth2?
OAuth 2.0 is designed only for authorization, for granting access to data and features from one application to another. … OpenID Connect enables scenarios where one login can be used across multiple applications, also known as single sign-on (SSO).
Is Basic Auth good?
Generally BASIC-Auth is never considered secure. Using it over HTTPS will prevent the request and response from being eavesdropped on, but it doesn’t fix the other structural security problems with BASIC-Auth. BASIC-Auth actually caches the username and password you enter, in the browser.
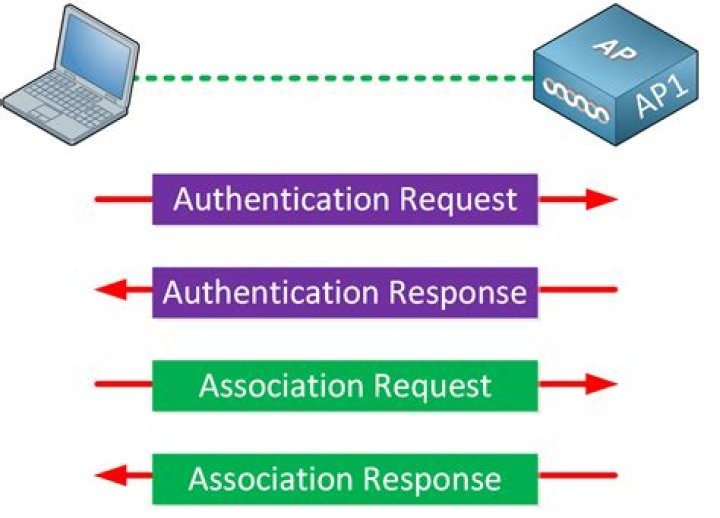
What is Open authentication wireless?
Open System Authentication (OSA) is a process by which a computer can gain access to a wireless network that uses the Wired Equivalent Privacy (WEP) protocol. With OSA, a computer equipped with a wireless modem can access any WEP network and receive files that are not encrypted.
What is OpenID provider?
An identity provider, or OpenID provider (OP) is a service that specializes in registering OpenID URLs or XRIs. OpenID enables an end user to communicate with a relying party. … An identity provider provides the OpenID authentication (and possibly other identity services).What is key clock?
Keycloak is an open source software product to allow single sign-on with Identity and Access Management aimed at modern applications and services.
What is the difference between OpenID and SAML?OpenID Connect is an open standard that organizations use to authenticate users. … SAML is an XML-based standard for exchanging authentication and authorization data between IdPs and service providers to verify the user’s identity and permissions, then grant or deny their access to services.
Article first time published onWhy OAuth is required?
OAuth is a delegated authorization framework for REST/APIs. It enables apps to obtain limited access (scopes) to a user’s data without giving away a user’s password. It decouples authentication from authorization and supports multiple use cases addressing different device capabilities.
What is Auth0 vs OAuth?
OAuth 2.0 is a protocol that allows a user to grant limited access to their resources on one site, to another site, without having to expose their credentials. Auth0 is an organisation, who manages Universal Identity Platform for web, mobile and IoT can handle any of them — B2C, B2B, B2E, or a combination.
What is SAML and OAuth?
Security assertion markup language (SAML) is an authentication process. Head to work in the morning and log into your computer, and you’ve likely used SAML. Open authorization (OAuth) is an authorization process. Use it to jump from one service to another without tapping in a new username and password.
What is OpenID vs OAuth?
Simply put, OpenID is used for authentication while OAuth is used for authorization. OpenID was created for federated authentication, meaning that it lets a third-party application authenticate users for you using accounts that you already have.
What is SAML v2?
SAML 2.0 is an XML-based protocol that uses security tokens containing assertions to pass information about a principal (usually an end user) between a SAML authority, named an Identity Provider, and a SAML consumer, named a Service Provider. … SAML 2.0 was ratified as an OASIS Standard in March 2005, replacing SAML 1.1.
Does SAML use LDAP?
SAML itself doesn’t perform the authentication but rather communicates the assertion data. It works in conjunction with LDAP, Active Directory, or another authentication authority, facilitating the link between access authorization and LDAP authentication.
How do I authenticate my WiFi?
- Toggle Airplane mode.
- Forget and reconnect to the Wi-Fi network.
- Reboot your Wi-Fi router.
- Change the network from DHCP to Static.
- Reset your network settings.
What are the benefits of open system authentication?
The open authentication method has no security whatsoever. If an STA can find and communicate with an AP, it will be allowed access. The advantage is the simplicity and ease, precisely because no setup is required.
What is the function of the wireless authentication?
Implementing authentication enables you to secure a network so that only users with the proper credentials can access network resources. It’s not an all-or-nothing deal, of course; you can use authentication to restrict or enable what a specific user can do once inside the network as well.
What is wrong with basic auth?
The worry about basic auth is that the credentials are sent as cleartext and are vulnerable to packet sniffing, if that connection is secured using TLS/SSL then it is as secure as other methods that use encryption.
Does Curl encrypt password?
- The password gets saved to the command history ( ~/. …
- On a shared system, it will usually be visible to others in ps , top and such, or by reading /proc/$pid/cmdline , for as long as the command is running.
Is HTTP Auth safe?
Note: The HTTP basic authentication scheme can be considered secure only when the connection between the web client and the server is secure. If the connection is insecure, the scheme does not provide sufficient security to prevent unauthorized users from discovering the authentication information for a server.
What is IDP?
Internally displaced persons (IDPs), according to the United Nations Guiding Principles on Internal Displacement, are “persons or groups of persons who have been forced or obliged to flee or to leave their homes or places of habitual residence, in particular as a result of or in order to avoid the effects of armed …
Why should I use Keycloak?
You may use Keycloak, if you need some Identity and User management platform, and when you have complicated user access flow. In the end, you could consider Keycloak, if you need SSO (Single Sign On) feature. Once logged-in to Keycloak, users don’t have to login again to access a different application.
What is Keycloak SSO?
Keycloak is an open source program that allows you to setup a secure single sign on provider. It supports multiple protocols such as SAML 2.0 and OpenID Connect. It can also store user credentials locally or via an LDAP or Kerberos backend.
Is OpenID Safe?
OpenID itself is secure, however due to its decentralised nature it often assumes that three servers are “trusted”. If these servers are not trustworthy then your security is gone.
What is the difference between authorization and authentication?
Simply put, authentication is the process of verifying who someone is, whereas authorization is the process of verifying what specific applications, files, and data a user has access to.
What is OAuth standard?
OAuth is an open-standard authorization protocol or framework that provides applications the ability for “secure designated access.” For example, you can tell Facebook that it’s OK for ESPN.com to access your profile or post updates to your timeline without having to give ESPN your Facebook password.
What is the difference between IdP and SP?
The identity provider (IdP) site is where the user is authenticated. The service provider (SP) site trusts the IdP and receives a SAML assertion to enable automatic login at the SP.
Can OIDC replace SAML?
While it’s possible that OIDC will replace SAML eventually, I’d just like to point out that we’ve finally got a serious snowball effect going with SAML. OIDC isn’t yet final, and it’s going to take time to migrate to.
What is Federation in security?
Definition of Federated Security. Federated security allows for clean separation between the service a client is accessing and the associated authentication and authorization procedures. Federated security also enables collaboration across multiple systems, networks, and organizations in different trust realms.