What is strong verification
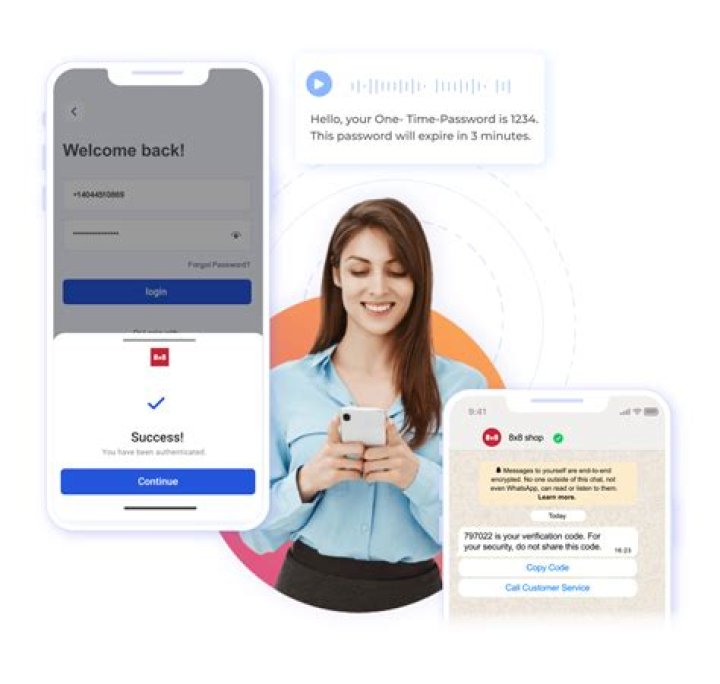
Strong Authentication is a method of user verification that is considered robust enough to withstand attacks on the system to which the users are authenticating. Strong authentication is thought to be true two-factor authentication or multi-factor authentication (2FA, MFA). …
What is considered strong authentication?
Strong Authentication is a method of user verification that is considered robust enough to withstand attacks on the system to which the users are authenticating. Strong authentication is thought to be true two-factor authentication or multi-factor authentication (2FA, MFA). …
What is an example of strong two-factor authentication?
A good example of two-factor authentication is the withdrawing of money from an ATM; only the correct combination of a bank card (something the user possesses) and a PIN (something the user knows) allows the transaction to be carried out.
How do you get strong authentication?
- Step 1: Password. The person creates and memorizes a unique set of numbers and letters used to access the system.
- Step 2: Possession. After typing in the correct password, a secondary string of letters and numbers is sent to the user’s registered smartphone.
- Step 3: Access.
Which of the following is the strongest authentication method?
What is Beyond Identity? Beyond Identity combines two of the strongest authenticators: biometrics and asymmetric keys. It eliminates the password and provides an extremely secure authentication since the user’s identity is only stored locally on the device and it cannot be moved.
Which authentication method is the most complex to administer?
Passwords. One of the most widespread and well-known methods of authentication are passwords. Passwords have been existing for a long time. However, it’s becoming more and more complicated to use password authentication as we have to create not one but a number of various passwords.
Why do you think strong authentication must make use of two or more means of proving identity?
Its purpose is to make attackers’ life harder and reduce fraud risks. If you already follow basic password security measures, two-factor authentication will make it more difficult for cyber criminals to breach your account.
Is SSO strong authentication?
SSO systems make it easy to authenticate the user once and thereafter be automatically authenticated when accessing related systems. Thus, SSO eliminates the hassle of separately signing on to multiple applications and systems. One set of login credentials is all the user needs.How do I build an authentication system?
- Get the username and password from user.
- Set it in request form params and send it to the server.
- Server validates the user based on the given username and password
- Once successful validation, create a cookie and set it in the response.
- The client then uses this cookie/session to make future requests.
Three-factor authentication – in addition to the previous two factors, the third factor is “something a user is.” Examples of a third factor are all biometric such as the user’s voice, hand configuration, a fingerprint, a retina scan or similar.
Article first time published onWhy is MFA needed?
Why is MFA Important? The main benefit of MFA is it will enhance your organization’s security by requiring your users to identify themselves by more than a username and password. While important, usernames and passwords are vulnerable to brute force attacks and can be stolen by third parties.
How safe is two-factor authentication?
It is not susceptible to common cyber threats. 2FA can be vulnerable to several attacks from hackers because a user can accidentally approve access to a request issued by a hacker without acknowledging it. This is because the user may not receive push notifications by the app notifying them of what is being approved.
Can 2 step verification be hacked?
Hackers can now bypass two-factor authentication with a new kind of phishing scam. … However, security experts have demonstrated an automated phishing attack that can cut through that added layer of security—also called 2FA—potentially tricking unsuspecting users into sharing their private credentials.
What are the three types of authentication?
Authentication factors can be classified into three groups: something you know: a password or personal identification number (PIN); something you have: a token, such as bank card; something you are: biometrics, such as fingerprints and voice recognition.
Which authentication is most secure?
Nowadays, the usage of biometric devices such as hand scanners and retinal scanners is becoming more common in the business environment. It is the most secure method of authentication.
Which type of biometric authentication is most secure?
Vein recognition or vascular biometrics takes the crown of being the most secure and accurate modality due to so many advantages it inherently offers. Vein pattern is not visible and collectable like facial features (and even fingerprints) but they are also not as hard to collect as retina pattern.
What are some examples of strong password requirements?
- At least 8 characters—the more characters, the better.
- A mixture of both uppercase and lowercase letters.
- A mixture of letters and numbers.
- Inclusion of at least one special character, e.g., ! @ # ? ] Note: do not use < or > in your password, as both can cause problems in Web browsers.
Is 2 step verification necessary?
Passwords, no matter how strong, may not actually be the best way to keep online accounts secure. Two-step verification, sometimes referred to as two-step authentication, reduces the chances of hackers or other outsiders gaining unauthorized access to your information.
What is Kerberos Key?
Kerberos is a computer network security protocol that authenticates service requests between two or more trusted hosts across an untrusted network, like the internet. It uses secret-key cryptography and a trusted third party for authenticating client-server applications and verifying users’ identities.
What are the 4 general forms of authentication?
- Password-based authentication. Passwords are the most common methods of authentication. …
- Multi-factor authentication. …
- Certificate-based authentication. …
- Biometric authentication. …
- Token-based authentication.
What happens first authorization or authentication?
In authentication process, the identity of users are checked for providing the access to the system. … Authentication is done before the authorization process, whereas authorization process is done after the authentication process.
Which server is used for authentication?
An authentication server is an application that facilitates authentication of an entity that attempts to access a network. Such an entity may be a human user or another server. An authentication server can reside in a dedicated computer, an Ethernet switch, an access point or a network access server.
What is OAuth server?
OAuth definition OAuth is an open-standard authorization protocol or framework that describes how unrelated servers and services can safely allow authenticated access to their assets without actually sharing the initial, related, single logon credential.
What is authorization in API?
Authorization refers to the process of verifying what a user has access to. … In authorization, a user or application is granted access to an API after the API determines the extent of the permissions that it should assign.
Is MFA same as SSO?
MFA and SSO are both coming at the issue of security and authentication from different areas. SSO is more convenient for users but has higher inherent security risks. MFA is more secure but less convenient. … Granting continued access to authenticated users throughout their workday.
Is SAML considered MFA?
MFA using SAML configuration As mentioned in a previous article, SAML is used for authentication and also it helps to enable SSO. SAML can also be used to configure MFA between different devices. In an enterprise where we have different SPs used by multiple hosts.
What is MFA and SSO?
Multi-Factor Authentication (MFA) and Single Sign On (SSO) are mechanisms to ensure your identity and access management setup is secure.
What are the 5 factors of authentication?
- Knowledge Factors. Knowledge factors require the user to provide some data or information before they can access a secured system. …
- Possession Factors. …
- Inherence Factors. …
- Location Factors. …
- Behavior Factors.
What is considered three factor authentication?
Three-factor authentication (3FA) is the use of identity-confirming credentials from three separate categories of authentication factors – typically, the knowledge, possession and inherence categories. Multifactor authentication dramatically improves security.
What is two way factor authentication?
Two-factor authentication (2FA) is a security system that requires two separate, distinct forms of identification in order to access something. The first factor is a password and the second commonly includes a text with a code sent to your smartphone, or biometrics using your fingerprint, face, or retina.
What is the risk of not having MFA?
Without multi-factor authentication (MFA), cybercriminals can much more easily gain access to an account. Once the username and password are acquired, every transaction will be treated as valid, and basic security measures cannot prevent it. Phishing is a worryingly easy method of stealing user data.